You hear the fans first. That high-pitched, desperate whine spinning up from the chassis of your laptop, or the sudden roar of your desktop cooling tower kicking into overdrive. Your mouse stutters. The keyboard input lags entirely. Then you hit Ctrl+Shift+Esc, hoping to catch a stray Chrome tab red-handed, only to find some completely unpronounceable executable chewing through thirty percent of your CPU and eating your battery alive.
- Decoding the Jargon: The Update Session Orchestrator
- A Sordid Tale from the Server Room
- Why Does It Hog So Much CPU and RAM?
- The “Hot Backpack” Syndrome: A Modern Standby Disaster
- Is It a Virus in Disguise?
- The Evolution of Background Patching
- How to Fix the Infinite Loop: A Step-by-Step Framework
- Advanced Diagnostics: Taming the Wake Timers
- WaaSMedic vs. MoUSO: The Battle of the Background Tasks
- Taking Back Control: Registry and Group Policy Tweaks
- The Shift to Windows 11
- Wrapping Up the Mystery
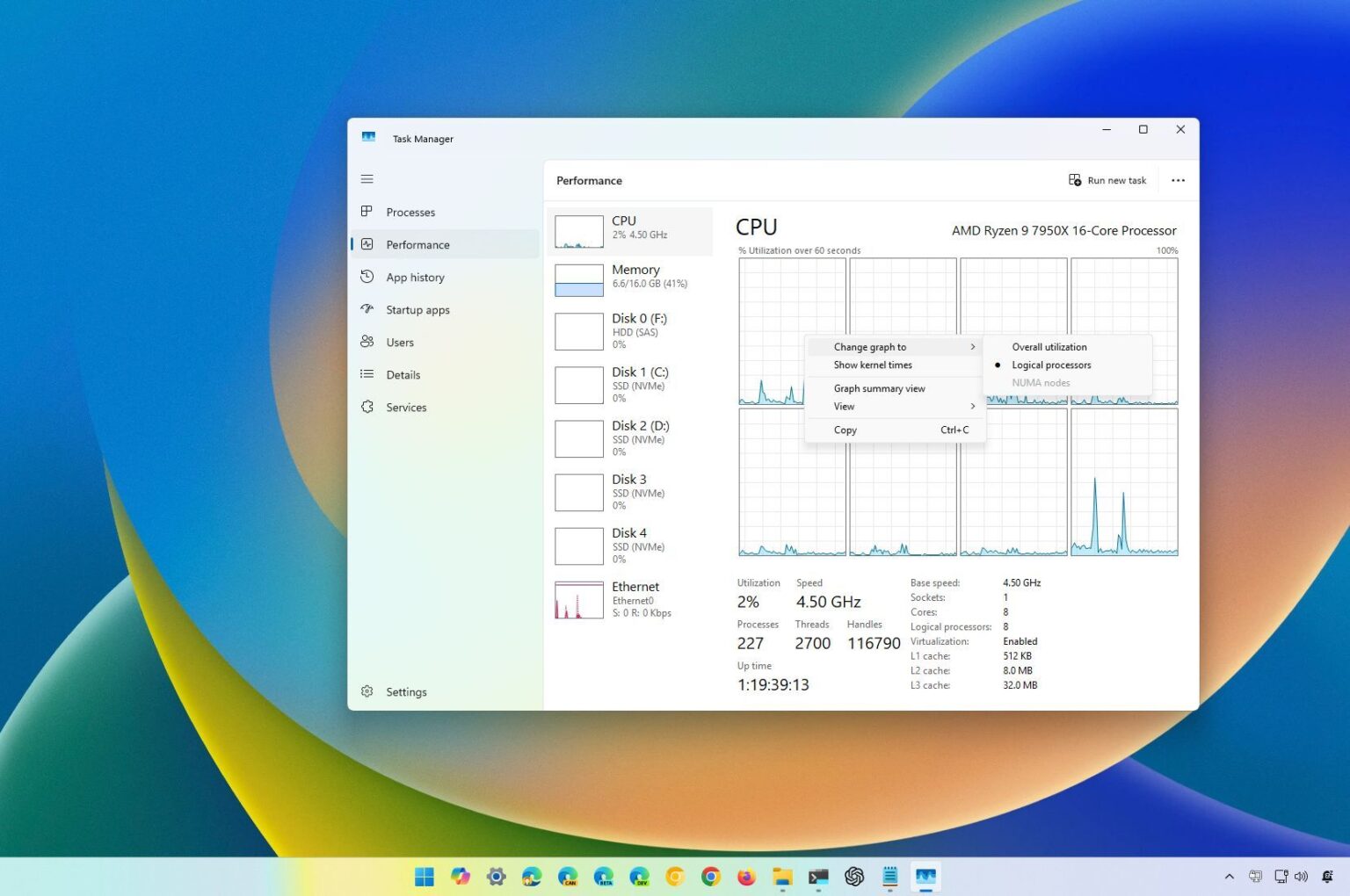
You stare at the screen, asking yourself: What is the MoUSO Core Worker Process in Task Manager?
You are definitely not alone in this exact moment of panic. Most people immediately assume they picked up a nasty cryptocurrency miner or some stealthy backdoor trojan. The name itself looks suspicious. It reads like a typo, a weird jumble of letters that does not immediately scream “Microsoft.” But before you right-click and forcefully kill the task—which, spoiler alert, usually just makes things worse—we need to talk about what this process actually does, why it suddenly decided to hijack your hardware, and how you can tame it.
Decoding the Jargon: The Update Session Orchestrator
Let us strip away the confusing acronym. MoUSO stands for Microsoft Update Session Orchestrator. The file you see running is technically named mousocoreworker.exe.
Think of this process as the highly stressed middle manager of your computer’s operating system. Its entire job is to coordinate the messy, complicated sequence of downloading, verifying, and installing Windows updates. Years ago, Microsoft relied on a different executable called wuauclt.exe (Windows Update AutoUpdate Client) to handle these chores. But as the operating system grew heavier and the patching sequence became vastly more complicated, the old architecture simply could not keep up.
The orchestrator was introduced to act as a traffic cop. It does not actually download the files itself. Instead, it wakes up, checks the current state of your system, talks to the Microsoft servers to see what patches are missing, and then barks orders at other underlying services—like the Background Intelligent Transfer Service (BITS) and Delivery Optimization—to actually go fetch the data.
When everything operates smoothly, you never even notice it running. It wakes up, does a quick handshake with the server, realizes you are fully patched, and goes back to sleep. The problem starts when the orchestrator encounters a roadblock.
A Sordid Tale from the Server Room
I know exactly how frustrating this executable can be because I have fought it on a massive scale. Whenever a panicked client sends me a frantic message asking, “What is the MoUSO Core Worker Process in Task Manager?”, my first question back is always about their recent patch history.
Back in late October 2021, I was overseeing a massive fleet migration for a mid-sized logistics firm. We were pushing out a critical cumulative security patch via Windows Server Update Services (WSUS) to roughly 140 client machines on a Tuesday night. By Wednesday morning, my phone was absolutely melting.
Dozens of users complained their machines were entirely locked up. I remoted into a primary workstation, pulled up the performance monitor, and watched in horror. The mousocoreworker.exe process was holding a staggering 12 gigabytes of RAM hostage. The disk queue length was pegged at a solid 50, meaning the hard drive was choking on read/write requests.
What happened? A specific error loop—technically an 0x800705b4 timeout code—caused the orchestrator to thrash the local storage. The system had downloaded a corrupted metadata file during the overnight sync. Instead of throwing a clean error and stopping, the orchestrator aggressively tried to read, parse, and apply that broken file thousands of times per second. It was a brute-force nightmare. We had to write a custom PowerShell script to forcefully flush the local update cache across the entire network just to get the office functioning again.
That is the reality of this process. It has incredible power over your system resources, and when it gets confused, it brings the whole machine down with it.
Why Does It Hog So Much CPU and RAM?
If you catch this process behaving badly, it is usually stuck in one of three distinct phases of the update lifecycle. Understanding these phases helps you figure out if you should intervene or just walk away and let it finish.
Phase 1: The Infinite Scan. Sometimes, the orchestrator connects to the update servers, but the connection drops for a microsecond, or the local registry keys tracking your current version get scrambled. The worker process will sit there spinning your CPU at 15% to 25%, endlessly comparing thousands of local files against the server manifest. It is like a librarian trying to inventory a massive library while someone keeps moving the books around.
Phase 2: The Installation Hand-off. When a major feature update is ready to install, the orchestrator has to prep the system. It checks your hard drive space, verifies driver compatibility, and unpacks heavily compressed files. Decompressing gigabytes of data is incredibly CPU-intensive. During this phase, seeing high disk usage and high CPU is completely normal. Interrupting it here is a terrible idea.
Phase 3: The Corrupted Cache Loop. This is the bad one. If a previous update failed midway through, the temporary files left behind become toxic. The orchestrator tries to resume the job, hits the broken file, fails, logs the failure, and instantly retries. This loop can eat up massive amounts of RAM as the process logs continuous errors into memory.
Resource Usage Thresholds: What is Normal?
To help you visualize whether your machine is just doing routine maintenance or actively having a meltdown, look at this breakdown of expected resource behavior.
| Process State | Expected CPU Usage | Expected RAM Usage | When to Worry (Red Flags) |
|---|---|---|---|
| Idle / Sleeping | 0% | Under 10 MB | If it uses any CPU while supposedly idle. |
| Scanning for Updates | 2% – 10% | 50 MB – 150 MB | Lasting longer than 15 minutes. |
| Prepping Installation | 15% – 30% | 200 MB – 500 MB | Disk usage at 100% for over an hour. |
| Stuck Error Loop | 30%+ (Constant) | 1 GB+ (Climbing continuously) | Fans blasting, UI freezing, endless high usage. |
The “Hot Backpack” Syndrome: A Modern Standby Disaster
If you are reading this because you immediately Googled What is the MoUSO Core Worker Process in Task Manager?, you probably have a laptop that sounds like a jet engine right now. But there is an even worse scenario that plagues mobile users.
Have you ever closed your laptop lid, shoved the machine into your backpack, and pulled it out an hour later only to find it dangerously hot to the touch? The battery is nearly dead, and the fans are screaming despite the lid being closed.
You can usually blame the MoUSO process for this.
Modern Windows machines use a power state called “Modern Standby” (S0 Low Power Idle). Unlike the old days where closing the lid actually put the computer into a deep, frozen sleep (S3 sleep), Modern Standby keeps the machine lightly awake, much like a smartphone. It does this so it can fetch emails, maintain a Wi-Fi connection, and—you guessed it—run background updates.
The orchestrator is heavily authorized to wake your hardware up. If it decides that 2:00 PM is the perfect time to install a massive cumulative update, it will pull the processor out of its idle state. Inside the confined, unventilated space of a backpack, the heat generated by the CPU unpacking gigabytes of update files has nowhere to go. The system thermally throttles, the fans spin at maximum velocity, and the battery drains to zero.
To stop this specific behavior, you have to dig into the command line and revoke the orchestrator’s wake privileges. We will get to that exact fix shortly.
Is It a Virus in Disguise?
Because the name looks so incredibly sketchy, it is natural to wonder if you have been infected. Malware developers are incredibly lazy, but they are also smart. They know that if they name their malicious executable super_virus.exe, your antivirus will nuke it instantly. So, they often name their payload after obscure, legitimate Windows processes to hide in plain sight.
You might see a fake MoUSO process running if your machine is compromised. Fortunately, verifying its authenticity takes about ten seconds.
Open Task Manager. Right-click on the MoUSO Core Worker Process and select “Open file location.”
A File Explorer window will pop up. Look at the address bar at the top. The legitimate, completely safe Microsoft file will always be located in exactly this directory:
C:\Windows\System32
If that window opens and you are looking at a file dumped inside your AppData folder, a random Downloads directory, or some heavily buried Temp folder, you have a massive problem. That is malware mimicking the orchestrator. In that scenario, you need to immediately sever your internet connection and run a heavy-duty offline scan using Windows Defender or Malwarebytes.
If it is sitting safely in the System32 folder, you can breathe a sigh of relief. It is not a virus. It is just Windows tripping over its own shoelaces.
The Evolution of Background Patching
To fully answer the question of What is the MoUSO Core Worker Process in Task Manager?, we have to look back at how Microsoft handled background tasks before the major 2020 architecture overhaul. Why did they even build this orchestrator in the first place?
Historically, Windows updates were a highly intrusive nightmare. A prompt would pop up in the middle of your screen demanding a restart. If you clicked away, it would just pop up again ten minutes later. It interrupted gaming, ruined presentations, and drove users insane. Microsoft realized they needed to make patching invisible.
They built the Update Session Orchestrator to monitor user behavior. It tracks your “Active Hours.” It watches your mouse movements and keyboard inputs. It tries to calculate the exact mathematical probability that you are going to step away from the keyboard for more than thirty minutes.
When it senses an opening, it strikes. It fires up the core worker process, downloads the files quietly, and pre-stages the installation so that the next time you manually reboot, the patch applies in seconds rather than minutes. It is a highly sophisticated piece of engineering. But like a sports car, when something misaligns in the engine bay, the resulting crash is spectacular.
How to Fix the Infinite Loop: A Step-by-Step Framework
Okay, enough theory. Your computer is currently lagging, the process is eating your RAM, and you need it to stop right now. Do not just hit “End Task.” If you forcefully terminate the orchestrator while it is writing a system file, you risk corrupting the entire registry, which can lead to the dreaded Blue Screen of Death on your next reboot.
We are going to perform a surgical strike on the update cache. This is the exact methodology I use on enterprise servers, and it works perfectly on home machines.
Step 1: Halt the Supporting Services
We cannot just delete the broken files while Windows is actively trying to use them. We have to shut down the supply chain first. You need to open the Command Prompt as an Administrator. (Click the Start button, type cmd, right-click the top result, and select Run as Administrator).
Once you see the black terminal window, you are going to type these exact commands, pressing Enter after each one. You will see a message saying the service is stopping, and then successfully stopped.
net stop wuauserv(This stops the main Windows Update service).net stop cryptSvc(This halts the cryptographic service that verifies file signatures).net stop bits(This kills the background downloader).net stop msiserver(This pauses the Microsoft Installer).
Step 2: Nuke the Corrupted Cache
Now that the services are asleep, the files they were holding hostage are unlocked. We are going to rename the two main folders where Windows stores pending updates. By renaming them, Windows will panic, assume they are missing, and completely rebuild a fresh, uncorrupted version of them from scratch.
Type these commands into the same terminal:
ren C:\Windows\SoftwareDistribution SoftwareDistribution.oldren C:\Windows\System32\catroot2 catroot2.old
Make sense, right? You are just slapping a “.old” extension on the folders to hide them from the operating system.
Step 3: Wake the System Back Up
Now we turn the supply chain back on. The system will generate brand new folders and the orchestrator will start with a completely clean slate.
net start wuauservnet start cryptSvcnet start bitsnet start msiserver
Type exit to close the terminal, and immediately reboot your computer. When you log back in, check Task Manager. The MoUSO process should be completely quiet, sitting at 0% CPU usage.
Advanced Diagnostics: Taming the Wake Timers
If your primary issue is the orchestrator waking your laptop up in the middle of the night, clearing the cache will not solve that. You have to revoke its power management permissions.
Windows has a hidden command-line utility for power diagnostics. Open up your Administrator Command Prompt again and type:
powercfg /waketimers
This command lists every single process that has permission to pull your hardware out of sleep mode. If you see MoUsoCoreWorker.exe listed there, you have found your culprit. To fix this, you have to dive into your advanced power plan settings.
Hit the Windows key and type “Edit power plan.” Click on “Change advanced power settings.” A tiny, old-school menu will pop up. Expand the “Sleep” category, and look for a setting called “Allow wake timers.” Change this setting to Disable for both “On battery” and “Plugged in.”
By throwing this switch, you are essentially telling the operating system: I do not care how important you think this patch is. If the lid is closed, the computer stays asleep. Period.
WaaSMedic vs. MoUSO: The Battle of the Background Tasks
While you are poking around in Task Manager, you might notice another weirdly named process eating up resources right next to our friend MoUSO. It is usually called WaaSMedicAgent.exe.
People often confuse the two, but they serve completely different, yet related, functions. WaaS stands for “Windows as a Service.” The Medic Agent is exactly what it sounds like—it is the doctor that Microsoft sends in when the orchestrator gets sick.
If the MoUSO process fails to complete an update three times in a row, the operating system flags a critical failure. It then wakes up the WaaSMedic process to scan the update registry, repair corrupted system files, and try to force the orchestrator back into a working state. If you see both of these processes running at high CPU simultaneously, your machine is actively having a severe internal software conflict. The cache-clearing fix I detailed above is the best way to resolve this digital fistfight.
Taking Back Control: Registry and Group Policy Tweaks
Some people—especially folks running audio production software, live streaming setups, or heavy rendering rigs—simply cannot afford to have a background process spontaneously decide to chew up 20% of their CPU. They need absolute, dictatorial control over their hardware.
If you are running Windows Pro, Enterprise, or Education editions, you can use the Group Policy Editor to leash the orchestrator permanently. This does not break your computer, but it does shift the responsibility of patching entirely onto your shoulders.
Open the Run dialog (Windows Key + R) and type gpedit.msc.
Navigate through this specific tree: Computer Configuration > Administrative Templates > Windows Components > Windows Update.
Look for the policy named “Configure Automatic Updates.” If you double-click it, you can change the state to “Enabled,” and then alter the dropdown menu to “2 – Notify for download and auto install.”
This is the holy grail setting for power users. It strips the orchestrator of its autonomy. It is no longer allowed to pre-fetch gigabytes of data in the background. Instead, it will just ping the server, see an update exists, and put a tiny, polite icon in your system tray. It will not download a single kilobyte until you explicitly click the button giving it permission.
If you are on Windows Home edition, you do not have the Group Policy Editor, but you can achieve a similar result by setting your Wi-Fi or Ethernet connection as a “Metered Connection” in your network settings. The orchestrator is programmed to respect data caps. If it thinks you are paying for data by the megabyte, it will pause all background downloading automatically.
The Shift to Windows 11
You might be wondering if any of this changes if you upgrade your operating system. Microsoft absolutely learned some hard lessons from the way Windows 10 handled background tasks. In Windows 11, the underlying architecture has been significantly refined.
The orchestrator still exists in Windows 11. You will still see it in Task Manager. However, its aggression algorithms have been heavily dialed back. Windows 11 relies much more heavily on “Delivery Optimization,” a peer-to-peer sharing system. Instead of the orchestrator brute-forcing a download directly from Microsoft’s swamped servers, it quietly asks other PCs on your local network if they already have the files.
Furthermore, the way updates are packaged has changed. The patches are physically smaller, meaning the decompression phase—the part that causes your CPU to overheat—takes a fraction of the time it used to.
That being said, a corrupted cache is still a corrupted cache. The exact same error loops that plagued IT departments in 2020 can still happen today. The troubleshooting steps remain identical.
Wrapping Up the Mystery
Let us finally put the mystery to rest. The next time a colleague looks over your shoulder, points at the screen, and asks What is the MoUSO Core Worker Process in Task Manager?, you can confidently explain the background orchestration mechanics without skipping a beat.
You do not need to fear it. It is not a hacker stealing your banking details, and it is not a cryptominer burning out your graphics card. It is just a highly complex, sometimes clumsy piece of software trying its absolute best to keep your operating system patched and secure.
When it behaves, let it run. It will finish its chores and disappear back into the digital ether. But when it stalls out, starts burning your battery, and locking up your mouse, you now have the exact command-line knowledge required to shut it down, clear out the bad data, and force it to start fresh. You are back in control of your hardware.